Android Security Analysis Tools, part two - DIVA app and AndroBugs
Contents
This article is part of a series:
Android Security Analysis Tools, part one - JAADAS
Android Security Analysis Tools, part two - DIVA app and AndroBugs
Android Security Analysis Tools, part three - Drozer and QARK
Android Security Analysis Tools, part four - MobSF
In the previous article, we began our exploration of security testing in Android applications. We started by discussing the testing problem and analyzing the first testing tools suggested by OWASP Mobile Testing Guide (MSTG). In this chapter, we will focus on the next tool for static security analysis suggested by MSTG - AndroBugs.
Benchmark
Before we get to the analysis tool, we should discuss one important matter - benchmarks. Having a reference point is a critical aspect of security testing. That kind of reference will introduce the testing context and provide the data that our results can be compared with. It is especially important at the reviewer’s training stage. The reference point can help to better understand the testing context and the scope of the expected results. The problem is finding a good benchmark. Such a benchmark will be a visualisation of a complex or interesting case which will make it more valuable for the testers. As an example, for mobile security testing, we can use the DIVA project.
The DIVA
DIVA, aka the Damn Insecure and Vulnerable App, is an Android application designed and created by Payatu. The app is designed in such way as to be extremely insecure. It was created to teach developers, QA, pentesters, students, etc. about potential vulnerabilities in Android Applications. It contains several common vulnerabilities, issues and bad coding practices covering both JAVA and native code.
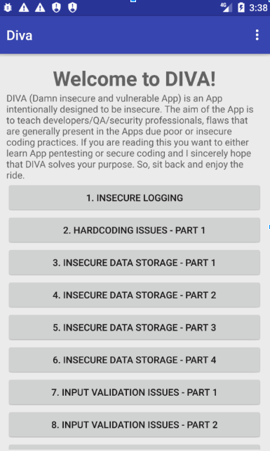
The app contains several issues on different levels like:
- Insecure logging,
- Insecure data storage,
- Access control issues,
- Hardcoding issues,
- Validation issues,
- Permissions misuse,
- Manifest issues,
- ...and many more.
DIVA is published under the GNU GPL v3.0 license, so you can use it as a benchmark for your experiments or just to improve your skills. We used it to create all the examples for this series of articles. Here are some useful links related to DIVA:
- GitHub - https://github.com/payatu/diva-android
- APK file - Payatu
- Payatu’s web page - Payatu
AndroBugs
AndroBugs is the second tool discussed in our series. According to the author, AndroBugs is a security testing framework for Android apps that was designed to help developers (or hackers) to find security vulnerabilities. The framework has been written in Python and published under the GNU General Public License v3.0. One very important piece of information is that AndroBugs works directly on the APK file. This means that you don’t need to have root permissions on your device to analyze an app. You don’t even need to have a device. The AndroBugs framework contains several security features:
- Security vulnerability searching,
- Best practices verification,
- Dangerous command verification,
- Massive analysis (multiple apps analysis at one time).
To run AndroBugs you need to fulfill only one requirement: having Python 2.7.x installed. There is also an additional requirement if you want to use Massive Analysis. To use this feature you need to have the PyMongo library installed. Massive Analysis is a mode of the AndroBugs framework that allows you to run an analysis for a large number of apps at the same time. The Mongo database is used to optimise analysis and save results. Later you can easily filter results in multiple ways using filtering commands.
To run the AndroBugs in basic analysis mode you can use this command:
python androbugs.py ./APKs/diva-beta.apk
For MassiveAnalysis just use this command line:
python AndroBugs_MassiveAnalysis.py -b 20181010 -t TestTag -d ~/APKs/
-o ~/Massive_Analysis_Reports
where
python AndroBugs_MassiveAnalysis.py -b [Your_Analysis_Number]
-t [Your_Analysis_Tag] -d [APKs input directory] -o [Report output directory]
Output
Below you can find an example output file that was generated by the AndroBugs framework. As you can see, the output is split into three main sections.
The first section contains basic information about the analysed app. There, you can find data like package name, version and build name, both SDK versions (minimum and target), and fingerprints of the APK file.
Under the basic info section, you can find the main result of the analysis. The next section contains a list of detected vulnerabilities. Each of them is classified with a predefined severity level. This classification can be very useful for reviewers. It will allow them to group detected vulnerabilities and prioritize tasks related to them.
Moreover, each item contains more detailed information about the detected issue. There, you can find a description of the issue with links to articles with an elaborate description of the issue. The description can also contain a link to the part of the source code where the issue was found. Unfortunately, the links only appear for Smali code, so to find the exact method you need to manually perform decompilation.
The last section of the result file contains simple analysis statistics and analysis time. Below you can find the results of the analysis of the DIVA app.
*************************************************************************
** AndroBugs Framework - Android App Security Vulnerability Scanner **
** version: 1.0.0 **
** author: Yu-Cheng Lin (@AndroBugs, http://www.AndroBugs.com) **
** contact: androbugs.framework@gmail.com **
*************************************************************************
Platform: Android
Package Name: jakhar.aseem.diva
Package Version Name: 1.0
Package Version Code: 1
Min Sdk: 15
Target Sdk: 23
MD5 : 82ab8b2193b3cfb1c737e3a786be363a
SHA1 : 27e849d9d7b86a3a3357fb3e980433a91d416801
SHA256: 5cefc51fce9bd760b92ab2340477f4dda84b4ae0c5d04a8c9493e4fe34fab7c5
SHA512: 86deea160864e4d48890b1e788e3ccc43bdd1d5a8c46d729d658b768093d4a3767d2bd885b7e5c722935f5ae477db415c62157943c0441dc64df7455d2a9cd25
------------------------------------------------------------
[Critical] Android Debug Mode Checking:
DEBUG mode is ON(android:debuggable="true") in AndroidManifest.xml. This is very dangerous. The attackers will be able to sniffer
the debug messages by Logcat. Please disable the DEBUG mode if it is a released application.
[Critical] AndroidManifest ContentProvider Exported Checking:
Found "exported" ContentProvider, allowing any other app on the device to access it (AndroidManifest.xml). You should modify the
attribute to [exported="false"] or set at least "signature" protectionalLevel permission if you don't want to.
Vulnerable ContentProvider Case Example:
(1)https://www.nowsecure.com/mobile-security/ebay-android-content-provider-injection-vulnerability.html
(2)http://blog.trustlook.com/2013/10/23/ebay-android-content-provider-information-disclosure-vulnerability/
(3)http://www.wooyun.org/bugs/wooyun-2010-039169
provider => jakhar.aseem.diva.NotesProvider
[Warning] External Storage Accessing:
External storage access found (Remember DO NOT write important files to external storages):
=> Ljakhar/aseem/diva/InsecureDataStorage4Activity;->saveCredentials(Landroid/view/View;)V (0x26) --->
Landroid/os/Environment;->getExternalStorageDirectory()Ljava/io/File;
[Warning] AndroidManifest Exported Components Checking:
Found "exported" components(except for Launcher) for receiving outside applications' actions (AndroidManifest.xml).
These components can be initilized by other apps. You should add or modify the attribute to [exported="false"] if you don't want
to.
You can also protect it with a customized permission with "signature" or higher protectionLevel and specify in
"android:permission" attribute.
activity => jakhar.aseem.diva.APICredsActivity
activity => jakhar.aseem.diva.APICreds2Activity
[Warning] WebView Local File Access Attacks Checking:
Found "setAllowFileAccess(true)" or not set(enabled by default) in WebView. The attackers could inject malicious script into
WebView and exploit the opportunity to access local resources. This can be mitigated or prevented by disabling local file system
access. (It is enabled by default)
Note that this enables or disables file system access only. Assets and resources are still accessible using file:///android_asset
and file:///android_res.
The attackers can use "mWebView.loadUrl("file:///data/data/[Your_Package_Name]/[File]");" to access app's local file.
Reference: (1)https://labs.mwrinfosecurity.com/blog/2012/04/23/adventures-with-android-webviews/
(2)http://developer.android.com/reference/android/webkit/WebSettings.html#setAllowFileAccess(boolean)
Please add or modify "yourWebView.getSettings().setAllowFileAccess(false)" to your WebView:
Ljakhar/aseem/diva/InputValidation2URISchemeActivity;->onCreate(Landroid/os/Bundle;)V
[Warning] WebView Potential XSS Attacks Checking:
Found "setJavaScriptEnabled(true)" in WebView, which could exposed to potential XSS attacks. Please check the web page code
carefully and sanitize the output:
=> Ljakhar/aseem/diva/InputValidation2URISchemeActivity;->onCreate(Landroid/os/Bundle;)V (0x2e) --->
Landroid/webkit/WebSettings;->setJavaScriptEnabled(Z)V
[Notice] AndroidManifest Adb Backup Checking:
ADB Backup is ENABLED for this app (default: ENABLED). ADB Backup is a good tool for backing up all of your files. If it's open
for this app, people who have your phone can copy all of the sensitive data for this app in your phone (Prerequisite: 1.Unlock
phone's screen 2.Open the developer mode). The sensitive data may include lifetime access token, username or password, etc.
Security case related to ADB Backup:
1.http://www.securityfocus.com/archive/1/530288/30/0/threaded
2.http://blog.c22.cc/advisories/cve-2013-5112-evernote-android-insecure-storage-of-pin-data-bypass-of-pin-protection/
3.http://nelenkov.blogspot.co.uk/2012/06/unpacking-android-backups.html
Reference: http://developer.android.com/guide/topics/manifest/application-element.html#allowbackup
[Notice] <#CVE-2011-3901#> Android SQLite Databases Vulnerability Checking:
This app is using Android SQLite databases but it's "NOT" suffering from SQLite Journal Information Disclosure Vulnerability.
[Notice] Native Library Loading Checking:
Native library loading codes(System.loadLibrary(...)) found:
[libdivajni.so]
=> Ljakhar/aseem/diva/DivaJni;->()V (0x4) ---> Ljava/lang/System;->loadLibrary(Ljava/lang/String;)V
[Info] Runtime Command Checking:
This app is not using critical function 'Runtime.getRuntime().exec("...")'.
[Info] Executing "root" or System Privilege Checking:
Did not find codes checking "root" permission(su) or getting system permission (It's still possible we did not find out).
[Info] SQLiteDatabase Transaction Deprecated Checking:
Ignore checking "SQLiteDatabase:beginTransactionNonExclusive" because your set minSdk >= 11.
[Info] Android SQLite Databases Encryption (SQLite Encryption Extension (SEE)):
This app is "NOT" using SQLite Encryption Extension (SEE) on Android (http://www.sqlite.org/android) to encrypt or decrpyt
databases.
[Info] Android SQLite Databases Encryption (SQLCipher):
This app is "NOT" using SQLCipher(http://sqlcipher.net/) to encrypt or decrpyt databases.
[Info] Dynamic Code Loading:
No dynamic code loading(DexClassLoader) found.
[Info] File Unsafe Delete Checking:
Did not detect that you are unsafely deleting files.
[Info] <#BID 64208, CVE-2013-6271#> Fragment Vulnerability Checking:
Did not detect the vulnerability of "Fragment" dynamically loading into "PreferenceActivity" or "SherlockPreferenceActivity"
[Info] Framework - MonoDroid:
This app is NOT using MonoDroid Framework (http://xamarin.com/android).
[Info] Base64 String Encryption:
No encoded Base64 String or Urls found.
[Info] Key for Android SQLite Databases Encryption:
Did not find using the symmetric key(PRAGMA key) to encrypt the SQLite databases (It's still possible that it might use but we
did not find out).
[Info] Codes for Checking Android Debug Mode:
Did not detect codes for checking "ApplicationInfo.FLAG_DEBUGGABLE" in AndroidManifest.xml.
[Info] APK Installing Source Checking:
Did not detect this app checks for APK installer sources.
[Info] KeyStore File Location:
Did not find any possible BKS keystores or certificate keystore file (Notice: It does not mean this app does not use keysotre):
[Info] KeyStore Protection Checking:
Ignore checking KeyStore protected by password or not because you're not using KeyStore.
[Info] Code Setting Preventing Screenshot Capturing:
Did not detect this app has code setting preventing screenshot capturing.
[Info] Getting Signature Code Checking:
Did not detect this app is checking the signature in the code.
[Info] HttpURLConnection Android Bug Checking:
Ignore checking "http.keepAlive" because you're not using "HttpURLConnection" and min_Sdk > 8.
[Info] KeyStore Type Checking:
KeyStore 'BKS' type check OK
[Info] Google Cloud Messaging Suggestion:
Nothing to suggest.
[Info] <#CVE-2013-4787#> Master Key Type I Vulnerability:
No Master Key Type I Vulnerability in this APK.
[Info] App Sandbox Permission Checking:
No security issues "MODE_WORLD_READABLE" or "MODE_WORLD_WRITEABLE" found on 'openOrCreateDatabase' or 'openOrCreateDatabase2' or
'getDir' or 'getSharedPreferences' or 'openFileOutput'
[Info] AndroidManifest Dangerous ProtectionLevel of Permission Checking:
No "dangerous" protection level customized permission found (AndroidManifest.xml).
[Info] AndroidManifest PermissionGroup Checking:
PermissionGroup in permission tag of AndroidManifest sets correctly.
[Info] Implicit Service Checking:
No dangerous implicit service.
[Info] AndroidManifest "intent-filter" Settings Checking:
"intent-filter" of AndroidManifest.xml check OK.
[Info] AndroidManifest Normal ProtectionLevel of Permission Checking:
No default or "normal" protection level customized permission found (AndroidManifest.xml).
[Info] <#CVE-2013-6272#> AndroidManifest Exported Lost Prefix Checking:
No exported components that forgot to add "android:" prefix.
[Info] Getting IMEI and Device ID:
Did not detect this app is getting the "device id(IMEI)" by "TelephonyManager.getDeviceId()" approach.
[Info] Getting ANDROID_ID:
Did not detect this app is getting the 64-bit number "Settings.Secure.ANDROID_ID".
[Info] Codes for Sending SMS:
Did not detect this app has code for sending SMS messages (sendDataMessage, sendMultipartTextMessage or sendTextMessage).
[Info] AndroidManifest sharedUserId Checking:
This app does not use "android.uid.system" sharedUserId.
[Info] SSL Implementation Checking (Verifying Host Name in Custom Classes):
Self-defined HOSTNAME VERIFIER checking OK.
[Info] SSL Implementation Checking (Verifying Host Name in Fields):
Critical vulnerability "ALLOW_ALL_HOSTNAME_VERIFIER" field setting or "AllowAllHostnameVerifier" class instance not found.
[Info] SSL Implementation Checking (Insecure component):
Did not detect SSLSocketFactory by insecure method "getInsecure".
[Info] SSL Implementation Checking (HttpHost):
DEFAULT_SCHEME_NAME for HttpHost check: OK
[Info] SSL Connection Checking:
Did not discover urls that are not under SSL (Notice: if you encrypt the url string, we can not discover that).
[Info] SSL Implementation Checking (WebViewClient for WebView):
Did not detect critical usage of "WebViewClient"(MITM Vulnerability).
[Info] SSL Certificate Verification Checking:
Did not find vulnerable X509Certificate code.
[Info] Unnecessary Permission Checking:
Permission 'android.permission.ACCESS_MOCK_LOCATION' sets correctly.
[Info] Accessing the Internet Checking:
No HTTP-related connection codes found.
[Info] AndroidManifest System Use Permission Checking:
No system-level critical use-permission found.
[Info] <#CVE-2013-4710#> WebView RCE Vulnerability Checking:
WebView addJavascriptInterface vulnerabilities not found.
------------------------------------------------------------
AndroBugs analyzing time: 1.788441 secs
Total elapsed time: 8.562675 secs
PROS
- Elements grouped by severity: Critical, Warning, Notice, Info
- Operating on Smali code (no source code needed)
- Contains several, hardcoded vectors of vulnerabilities (searching for vectors in code)
- Optimized searching
- Searching for suspicious fragments of code and then checking the method execution context
- Massive analysis (many apps in one run)
- No root access needed
- No additional client app needed on the device
- Extensive analysis
Cons
- Not maintained
- The last commit to the repository was published over 3 years ago
- Many false positives - from tools or Google libs
- It can make review process more complex especially when the tool is used in automatized process;
- Integration is more complex in basic setup
- Basic output file is raw text,
Summary
AndroBugs is another static analysis tool suggested by OWASP MSTG for checking the security of Android apps. It is a very easy-to-use but effective tool. It is based on Python scripts and it seems to be very precise. A very important aspect is the fact that analysis is based on predefined vectors. You can also add your own vectors. Thanks to this feature you can easily extend detection capabilities. Vulnerability vectors are also the base of the optimization engine which, together with Massive Analysis mode, can significantly reduce the time of the analysis, especially when working on multiple applications at once.
Another important element is the output and the information that it holds. The most important feature of the output file is severity classification. In my opinion, it can make the work of the reviewer much easier. Unfortunately, the output file is presented as plain text. The lack of a defined structure (like in JAADAS) can significantly inhibit integration with other tools in your CI/CD stack.
However, the biggest drawback is, in my opinion, the fact that the tool is not maintained. The last commit to the repository was published almost three years ago. Four versions of Android have been released since then. This is very important due to the fact that all of these versions contain major updates related to security. In my opinion, the vector set should be updated with adjustments to new versions of the Android SDK. Unfortunately, this requires additional work. This, in turn, may disqualify AndroiBugs as a tool that can be easily and quickly integrated with your existing CI/CD stack.
Other articles from this series:
Android Security Analysis Tools, part one - JAADAS
Android Security Analysis Tools, part three - Drozer and QARK
Android Security Analysis Tools, part four - MobSF
Photo by Viviana Rishe on Unsplash
